Action required: security breach detected by PrestaShop (March 2020)

A security breach has been found by PrestaShop in versions 1.7.0.0 up to 1.7.6.3
Is this a critical flaw that can impact my business?
Yes, this flaw allows any hacker to modify customer's addresses and personal information.
Malicious robots are currently looking for sites that has this flaw, time is ticking to get protected.
How do I know if I'm vulnerable?
We've just published a FixMyPrestaShop update integrated to Store Commander (2020-03-09) that you can apply via Sc interface > Help > Update.
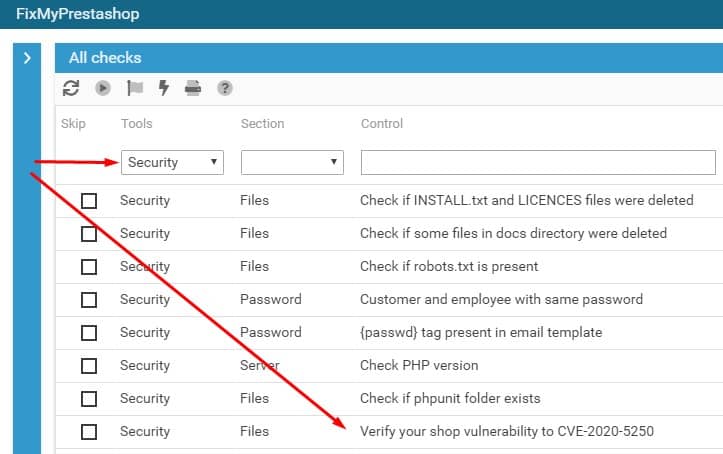
Then open FixMyPrestaShop from Sc interface > Tools menu.
Look for the control under Tools > Security > Verify your shop vulnerability to CVE-2020-5250
Run the scan of this control (Play button on the toolbar).
Once the control has been scanned, you either get:
- OK: everything is fine for you, phew!
- ERROR: we show you the problems detected
How to be protected?
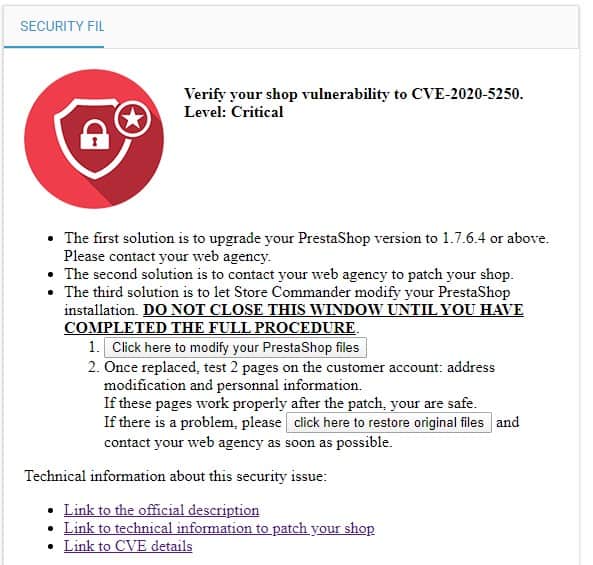
If you get ERROR, the right handside panel in FixMyPrestaShop offers you several solutions.
Is the protection definitive?
Yes, the fix is definitive but some security checks in FixMyPrestaShop need to be run regularly. That's why it's important to scan your shop with FixMyPrestaShop tool every so often.
This tool is available in all our offers at no extra cost because it is essential: more than a hundred checkpoints are verified on your shop.
What does the protection of FixMyPrestaShop technically do?
The tool detects the PrestaShop version of the shop, then depending on the version used (1.7.0, 1.7.1, 1.7.2, 1.7.3, 1.7.4, 1.7.5 or 1.7.6), backs up and replaces 4 files of the installation in the folder "/classes/form/" (provided that no override is detected). In case of override detected, it is possible to go back in order to let an agency study technically the solution. This action is sufficient to protect against the vulnerability.
On the other hand, it does not change the front office of the shop. A patch is necessary to correct a minor malfunction: when editing an address in the ordering process, this address can be duplicated rather than modified. Your agency can fix this problem with this Git commit 2.
More technical information for developers:
- Official PrestaShop post on the Build blog
- GitHub Security Advisory: GHSA-mhfc-6rhg-fxp3 and Git commit 1 (included in 1.7.6.4), Git commit 2 (included in 1.7.7.0)
- CVE reference: CVE-2020-5250
Advantages of using FixMyPrestaShop:
- No additional module to install
- All the technical work is done in 1 click to save a considerable amount of time (4 files * 8 versions required = 32 manipulations available in 1 click)
- Possibility to go back in 1 click
- Scanning your shop regularly allows you to check all the security elements and not only this flaw, to make sure that the shop is secure.